The choice of a bare metal server depends on many factors, including pricing, financial forecasts, application needs, risk level, and future IT requirements.
Typically, bare-metal servers are more costly than traditional hosting plans. It’s, therefore, vital to review your budget. How much are you willing to spend on the server?
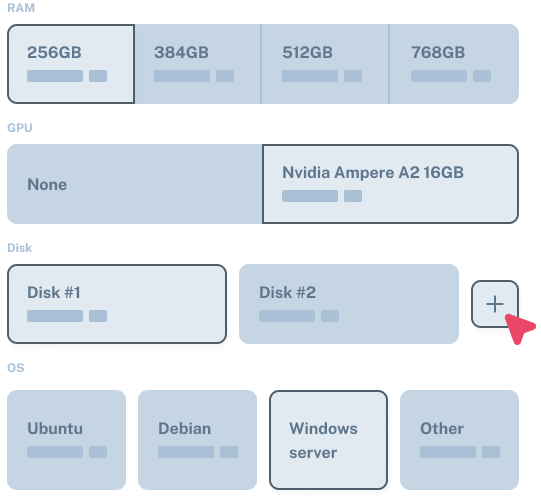
Determine performance requirements. Will the server’s hardware resources and processing power deliver the expected performance for your business?
Also, the amount of data generated and stored should be considered. This will inform the amount of storage to provision and the nature of data storage (SSD or NVMe).
Equally important is evaluating your security requirements. To safeguard against data breaches, consider critical security add-ons such as DDoS protection and firewalls.
.png?id=1758550628)